NO MONKEY ACADEMY
SAP Security Training for Business-Critical Landscapes
Cybersecurity can’t be left to processes and technology alone – it needs human input, too. When it comes to safeguarding your SAP landscape, one of the most valuable assets you possess is your employees.
The way we see it, organizations have two choices, rely on reactive strategies, outdated controls, protection-software technologies, and third-party vendors to safeguard their crown jewels, OR start cultivating the knowledge and expertise internally that close critical skill gaps, reduce enterprise risk, and improve your security posture.
NO MONKEY ACADEMY offers SAP Security training specific to the needs of different departments, teams, and job roles. Let us help you reduce knowledge gaps while unifying your SAP security lines of defense to become resilient against cyber threats and attacks.
Choose the SAP Cybersecurity Trainings That Fit Your Needs
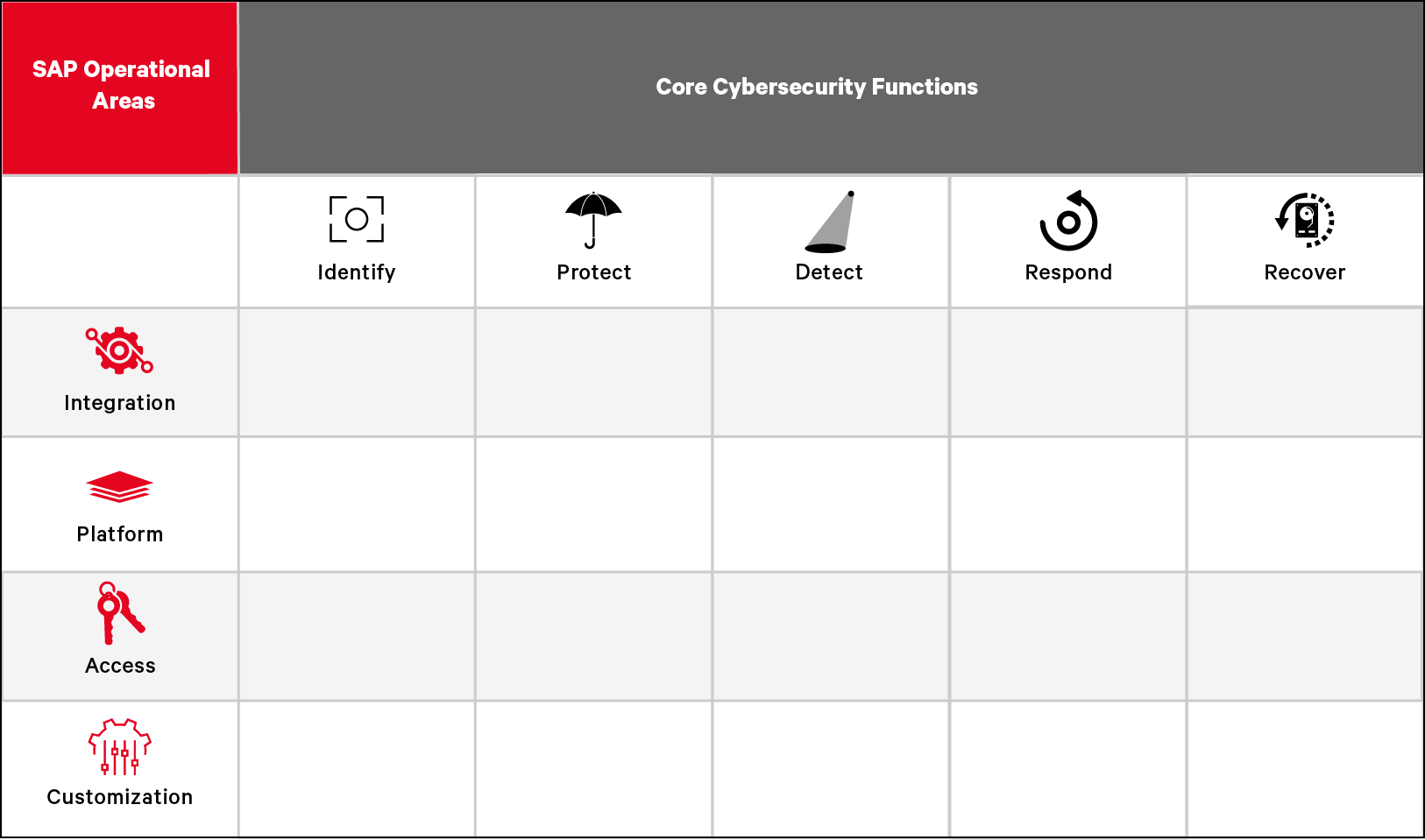
NO MONKEY Security Matrix
An Easier Way to Choose Training Based on Your Work-Role and Job-Function
The NO MONKEY Security Matrix gives your organization a comprehensive way to upskill employees and eliminate SAP security gaps.
In the Security Matrix, each training is organized around two categories:
- The operational area of SAP technology you work with
- The five core cybersecurity functions from the National Institute of Standards (NIST) and Technology’s Cybersecurity Framework (CSF)
This makes it easier for teams and individual learners to identify security training topics most relevant to their role, job-function, and responsibilities.
SAP Security Bootcamp for Your SAP Operations, IT Security
and Audit Lines of Defense
and Audit Lines of Defense
Need major results fast? The quickest way to attain the competencies to protect and defend your SAP landscape is in an immersive classroom experience.
With a “learn-apply” approach, our Live Online Training offers interactive role-play, simulations, and assignments, together with a practice lab environment. Teaching from virtual classrooms, our expert trainers facilitate real-time discussions with and between learners.
The result? Participants gain a deeper understanding of SAP security – and can start applying it much sooner. Protecting SAP technology just got a whole lot easier!
What You’ll Get From NO MONKEY ACADEMY SAP Security Training
NO MONKEY Open Training Sessions
SAP Security Training for Smaller Teams and Individuals
Open Training Sessions offer a rotating schedule of the hottest SAP security topics for SAP Operations, IT Security and Audit teams and any other individuals who play a key role in protecting business-critical SAP landscapes.
Each session brings together peers from multiple organizations and departments to learn in a virtual classroom. The training sessions are designed to include not only the perspective of the attacker and defenders, but to address the multiple lines of defense and individual work-roles that must work together to form an empowered, silo-free defense against cyber threats.
How NO MONKEY ACADEMY Equips Your SAP Lines of Cyberdefense
NO MONKEY ACADEMY was built to help organizations holistically address SAP security training for their lines of cyber defense. To learn more, choose from an option below.
